
Overview
First of all, I still haven’t had my shot @ OSCP, and most of the online reviews I read about OSCE suggested that it’s better to clear OSCP first, and then take a dig at OSCE. Well, I took my chances and went straight for OSCE, as many of my peers suggested not to take OSCP, which in fact is a great certificate in itself, but mostly just the test of your googling skills as suggested by them. I had plans for taking OSCP since the last couple of years, but when had a choice to go for either OSCP or OSCE, I chose the big brother.
Before taking the certificate, I only had a basic understanding of buffer overflows, debuggers, memory etc. from a few vulnhub machines that I did in the free time last year, best of what I tried was Hades, after which I just took a break from reversing.
Dreaded reviews all over the internet, a high first time failure rate, and no experience with any of the Offensive Security examinations beforehand, it was safe to say that I was pretty nervous before signing up.
Registration
Registration was in itself a fun experience, as you just can’t go to their website and register for the course. Instead, you need to crack a challenge hosted by the OffSec guys, which needs you to find a Registration Code and a Secret Key, mandatory when registering for the course on their website. The challenge is a 2-step process, which if you are having too much difficulty to crack, you might have a hard time during the course. It took me about 3-4 hours to complete the challenge, of which the first one got completed in 20 minutes itself. After completing the challenge, I opted for a 60-day lab environment + Exam, and finalized the starting date to be 11th December. The waiting period started.
Course
The corresponding course for OSCE certification is CTP (Cracking the Perimeter), which is mandatory before taking the certification exam. The syllabus is available on their website, which discusses different exploitation techniques in great detail, and a few interesting case studies as well. The module presented is really small and fairly easy to my liking, which I completed in about a week’s time, as this was my plan, to complete the course first without diving deep into the topics, and after that start the research.
The first two modules discussing web application exploits were fairly easy and took me less than a couple of days to complete, as it’s my day to day job as well.
The next modules discussed backdooring and AV bypass techniques, was interesting, but then again, easy to understand. Do note that though the course just touches the surface for AV bypass techniques, when I dug deep into the topic, I was surprised to see so many ways to bypass even the most advanced and up-to-date antiviruses, all building upon the same technique discussed in the course.
The next two modules were where I felt the course was picking up the difficulty level, discussing techniques like ASLR bypass and egghunters. The topics were interesting, and I thoroughly enjoyed these modules. Egghunters, in particular, is a really interesting topic, and makes numerous appearances in different modules for this course.
The case studies after that, discussing 0-day scenarios for TFTP and NNM, were the highlight of the course for me, and the most difficult part in the course. TFTP in itself took a whole day to complete, but NNM, that was a different beast, the hardest module in the course which took a full two days to complete. Most of my time on NNM was spent on building a custom python script to aid the process, but till the time the module was completed, my head was throbbing out of sheer difficulty of the topic.
The networking module in the end discusses a fairly new to me scenario of exploiting Cisco routers. This was OK, but the least interesting module in the whole course.
Many reviews I read online states that the course material is outdated, and it’d be good if Offensive Security updates it. And I partially agree with that, as the techniques discussed in the course would hardly scratch a surface on today’s Operating Systems, but as they say, You need to learn to walk first before you can run. The course builds up the base for exploitation, and as the course name suggests, it’s just for “Cracking the Perimeter”. The AWE course for OSEE seems to pickup those “running” techniques, and discusses Advanced Kernel Exploitation techniques. If I see the Offensive Security Suite as a whole, they have carefully placed the topics in each of the courses they provide, and for me, OSCE sits just in between the OSCP and OSEE.
The labs provided with the course are good, and contains just a handful of machines to practice on. For most of the course duration, I stayed away from the labs, and practiced on my local machines only. It took me about a month to complete everything in the course to the point where I felt, I was ready for the exam. Wanted to take the exam then only, but I thought that if I failed, it would hurt to see that a month of lab time was left and would have used that. Keeping that in mind, I chose to have the exam on the last day of my lab times, 8th February @ 7:30pm, not a very good time for most, as many suggested me to take a good sleep before attempting the exam.
Exam
Now comes the dreaded part, a gruesome 48-hour marathon of a exam, which contains different targets to be exploited for a total of 90 marks, out of which 75 are needed to pass the exam. The point system is distributed as such that you’d need to attempt each and every machine in the lab. My strategy was to attempt the lower marks targets first, and then move to the meaty ones, and if stuck somewhere, switch to the other machine. The exam started on 8th February at 7:30pm, exactly when OffSec guys sent the exam guidelines and the VPN connection details. It took me about an hour just to go through the guidelines and setup the connection. The objectives seemed fairly straightforward and easy to the eyes.
I picked up my first target, a low hanging fruit, and it was fairly simple. In a couple of hours, I was done with one machine. It boosted my confidence.
Went to the another low marking machine, and it was fairly easy as well. In an hour I completed 50% of it, then thought it’d be better if I just move to the bigger targets as this is feeling all too easy. I left it midway, and started with the bigger targets.
For hours now, I was just switching between these two targets, not able to make any progress. It was already 2 in the night, and I had already spent almost 4 hours in both of these machines with no output. I slept, and after a good long healthy sleep, woke up @ 9 next morning to pickup where I left.
In another 4 hours, I was able to make a good progress on one of the higher mark machine, the exploit that I wrote was working on my local setup. But, when I ran it on the actual server, it wasn’t working. I knew I had the solution, just missing a step somewhere here and there. Spent another hour to look into the issue, not able to find anything, I switched to the last machine, another big one. I was feeling tired, and hungry, so went out to refresh my mind and have something to eat.
Came back, and spent next 10 hours on this machine. In the first 3 hours, I got the entry point to the machine and was able to complete almost 90% of this machine, but for the remaining time, I was just struggling to make it 100%. I was trying everything, looking everywhere, but to no avail.
It was almost midnight, and I was exhausted. So close, I was almost just one step away in all of the machines, but somewhere I was making mistakes. Because of the tiredness, I almost forgot that I had the lower mark machine left @ 50% to be completed. I tried for another couple of hours to crack the bigger targets, nothing worked, so I slept.
Woke up @ 9 in the morning again, realizing that I have less than 12 hours now remaining for the exam. I was feeling frustrated, I was just one step away in every machine that was left, and I just couldn’t find that last step anywhere. I started with the lower mark machine that I left, and in an hour I cracked it. But it didn’t do anything, as I was still very far away from passing marks, and even though I was at the last step in the remaining machines, they still weren’t completed. But then:

As they say, this is infact where the best ideas comes to you. Just when I was sitting there, I realized what I might be doing wrong, quickly finished, and went to test my theories. And there it was, the stupidest mistake that made me almost kill myself in shame. This mistake costed me 6 hours last night and a lot of frustration, and there it was. After that, it was just an hour’s work before I cracked the system. I was happy, but far from relieved as still the last big target was left. I was again only at the last step on this target, just one thing I was missing somewhere. Less than 6 hours remaining, I knew I could find something, somewhere. In a couple of hours, I found what was missing. It wasn’t something very revolutionary, but I think that the frustration during exams makes you forget the most basic things to try. Then it just took me half hour to make modifications and there it was, all machines finally cracked with still 3 hours to go.
I was feeling happy, delighted, and slightly angry as well due to the fact that the exam would have been finished last night only had I not been stuck on that stupid mistake. Nevertheless, I spent the remaining time taking screenshots, collecting every evidence for the report before the lab time runs out.
Had a little celebration that night with friends, and after two exhaustive days, slept like a baby that night. Woke up the next day in noon, made the report, and submitted it to OffSec guys, hoping for a positive news from them as I cracked every machine in the exam.
Verdict
In the end I’d say this course is worth it. Just go for it. If you are very new to assembly, buffer overflows or reversing, 60 days lab would be good for you, but if you even know just the basics for these topics, which I see what OSCP offers, 30 days should be enough, though your mileage may vary. Whatever I learned from the course, it was in the first 30 days itself, the next 30 days were basically chilling out, and revising the already read topics. (and making this website as well in between :P)
The exam wasn’t as hard as I thought it would be, being this the first time I was facing the famous exam twists by Offensive Security, I could have completed it in under 24 hours had it not been for that small mistake. But don’t fool yourself into thinking that it will be easy, it still needs a lot of creative thinking to crack the machines, as the exam adds on to the topics that are discussed in the course, and would need a lot of research outside the course material before you can even think to have a go at it. Just going through the course materials and giving the exam would be a perfect recipe to fail.
Tips
For the labs:
- Go through the basic buffer overflow techniques, be familiar with a debugger and memory before taking up the course.
- Setup the labs locally beforehand as much as you can, sometimes the VPN connection is slow, which takes a toll on the time taken to complete the current task.
- Make sure to take regular notes of whatever you are doing, arranging them neatly greatly helps. I use KeepNote to take the notes.
- Automate anything you can, saves a lot of time, and might come handy in exams as well.
- Research, pick up random exploits from Exploit-DB, and recreate them without looking at current exploits.
- Don’t be just stuck on the module, learn as much as you can on the topics discussed in the module, the exam would be one step ahead of the topics discussed in the module.
For the exam:
- Make sure to have a good night sleep beforehand, believe me, I was in the office the whole day before attempting the exam, and it wasn’t easy to concentrate after a couple of hours.
- Have all the notes, scripts handy from the labs, in case you need to revisit a topic.
- Take regular breaks, concentrating on one thing for too long doesn’t help. Your brain do need refreshment once in a while.
- Don’t be stuck on one machine for too long, if you can, jump to another one, even if it seems harder than the one you are currently on.
- Manage your time. 🙂
Some references that you might find really useful for the course:
FuzzySecurity Windows Exploitation
Corelan Exploit Writing Tutorials
g0tmi1k’s blog –> One of the best reviews for OSCE, with a ton of relevant resources to take a look at.
Result
After waiting for 3 days, here it was, the confirmation of my achievement:
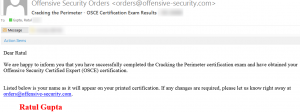

Happy, delighted, exhausted, and satisfied, I am ready to take on the next challenge, OSEE, hopefully soon when I have enough savings with me. (or if someone can sponsor me for that. :P)

I’m impressed…. by the time management of yours.
Looks like I wanna skip OSCP 😉
By d way. … congrats and good luck with OSEE. I suggest you :: keep that same 32_gig around for writing 0-days in EE. See ya soon. …!
Congratulations first and good to see more, on this blog soon. Gob bless you rats.
Great write up but I believe that yourself and friends are 100% wrong on oscp. If you take the oscp solo which by he sounds of it wouldn’t be the case in your situation, then there are a huge amount of areas that will test your metal. I have often seen arrogant comments around the cert only by people that didn’t sit it and oddly enough have a team of people around them thus avoiding individual efforts. I did the oscp first with no friends or colleagues in this are so was truly on my own sand can state in a good amount of cases it’s purely down to left field thinking which google can’t help you with.
That is true as well. I myself have tried certain OSCP machines, some vulnhub machines, internal CTFs inspired from OSCP machines, but found them to be fairly easy and straightforward once you get the path right. If I am not mistaken, OSCP is basically about the initial reconnaissance and exploiting using the pre available exploits, sometimes requiring some basic tweaks to work. Have heard about the machines like Pain, Sufference, Humble etc. to be much more challenging, but couldn’t try them at the time.
Though one of the main reasons for me to not take OSCP is it’s deteriorating market value due to people not even knowing basic knows-hows about security clearing it. The certificate in itself is a great experience for sure, but given the choice between OSCP and OSCE, I chose the later due to my interest in exploitation.
Hey..you said u practised locally ? Can you download all the exploitables to your machine ?
no, I mostly practiced with random exploits from exploit-db, searching for the specific sort of exploitation technique, and downloading appropriate software to recreate the exploit from scratch.
Hey are you taking AWE course this year?
Unfortunately, no.
Still looking for sponsors for that.